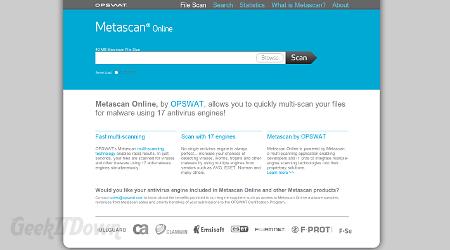
Metascan Online
Safety and security have become increasingly important in today’s computing age. Malware and viruses can worm their way in from a number of different sources and cause havoc on computer systems. Hopefully, everyone reading this uses an anti-virus of some sort and routinely scans their computers for infections.
The rule of thumb is one anti-virus per system. Any more than that and the computer can become unstable. However, there are times when one anti-virus might seem insufficient. Maybe you’re more paranoid than the average user or perhaps a certain file has raised a red flag. Either way, Metascan Online can help with those concerns.
Metascan Online is an online file scanning service which scans for infections. The service allows users to choose a file located on their local machine and have it scanned using the Metascan Online multiple engine process. The multiple engines are 17 different anti-virus software applications all used to scan the same file. The engines used include popular names such as Avast, AVG, ESET, McAfee and 13 other anti-virus software programs.
The scanning process is quick, but how quick depends on file size. Maximum file size allowed for scanning is 40MB. If server load is heavy, files are placed in a queue for ordered scanning. Results show a colored ring with the number of threats detected. For example, if the file is infection free, then a solid green ring is displayed with a 0/17 threats detected message. Along with threat information are other items such as file size, type and MD5 hash value. Each engine is listed to separate the results, display the scan time and last updated definition date. We found definitions are updated to within one day.
Metascan Online should not be used in place of traditional anti-virus software, but in conjunction with it can add an increased sense of security for times when files seem iffy. Metascan Online is free to use and made available by Opswat.
Visit Metascan Online
If you enjoyed or found this article useful, please show us some support by liking us on Facebook or by sharing us on your favorite social website. Thanks!