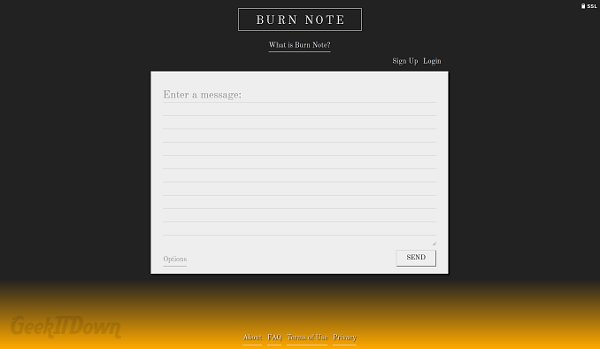
Burn Note
This message will self destruct in 3..2..1.! At least that’s the premise of Burn Note, a cloud based message service that sends messages between parties and deletes them after they’re read.
Burner Messages
Each message sent through Burn Note can be read only once. After which the message is deleted and essentially burned out of existence. Similar to burner phones where they can be discarded after single use, Burn Note messages are definitely deleted after a single read.
Notes are deleted either manually by the recipient or immediately upon navigation away from the message page. Senders have the option to set a timer on messages to further control the burn time. Burn Notes which go unread are automatically discarded after 72 hours.
Features
Burn Note is clearly meant as a security tool for sending sensitive and secure information between parties. To that end, other features are in place to ensure Burn Note remains as secret and secure as possible.
Short Phrases for example, makes copying and pasting of message contents impossible and makes taking screenshots of the message unbelievably troublesome, especially if the message has a short timer. Messages are broken down into snippets which appear individually on screen and rotate in order, every couple seconds.
The Spyglass feature hides the message entirely. Recipients can view the note by clicking and dragging a simulated flashlight across the screen to reveal the contents of the message.
Senders also have the option of placing their own password on the message for added security. Pending messages are stored encrypted on Burn Note servers and communication with Burn Note is done through 256 bit SSL encryption.
For the exceptionally security conscious, Burn Note provides detailed technical information about their storage and encryption methods on their website. Burn Note seems to have every angle covered aside from screen recording which is somewhat out of their control.
Summary
While not everyone will need Burn Note services, there is certainly a need for it. The internet is a wild west environment with unknowns around every corner. Sending information can be a somewhat unnerving process, but through Burn Note users can feel confident every precaution is being taken to protect their message data.
Aside from the obvious sharing of information between parties, we found this cloud tool to be somewhat fun which is hard to accomplish when utilizing security measures. Burn Note is great for spies or friends who just want to have a private undocumented conversation.
Visit Burn Note
If you enjoyed or found this article useful, please show us some support by liking us on Facebook or by sharing us on your favorite social website. Thanks!